Legacy System Modernization Strategies – How to Change Without Disrupting the Business
When an organization becomes aware of the risks associated with a legacy system, a seemingly simple question appears: Should we replace the system? In practice, this is the wrong question to start with. Legacy system modernization strategies are not a single scenario – they are a set of approaches that must be adapted to a specific business, technological, and organizational context. A better question is: Which strategy should we choose to reduce risk while enabling further development?
Strategy 1: Keep & Maintain
This is a conscious strategy – although it is often mistaken for “doing nothing”.
When does it make sense? Primarily when the system is stable and fulfills its purpose, it does not block key business initiatives, risks are known and controlled, the cost of change outweighs potential benefits.
What does it involve? It focuses on: monitoring and maintaining the system in its current form, minimal changes (bug fixes, security updates), clearly defining the system’s boundaries – what it will no longer be expected to do.
This is typically a temporary strategy used for systems nearing the end of their lifecycle. It allows organizations to manage the lifecycle consciously rather than reactively.
Strategy 2: Technological Modernization (Replatforming / Refactoring)
In this approach, the system remains in place, but the technical foundation changes. Replatforming a legacy system may include: upgrading technologies or frameworks, migrating to newer infrastructure, improving code quality, introducing automated testing and deployment processes.
Advantages: lower risk than a full replacement, business continuity preserved, improved stability and security.
Limitations: this strategy does not solve architectural or process-related problems, nor does it change the underlying business logic.
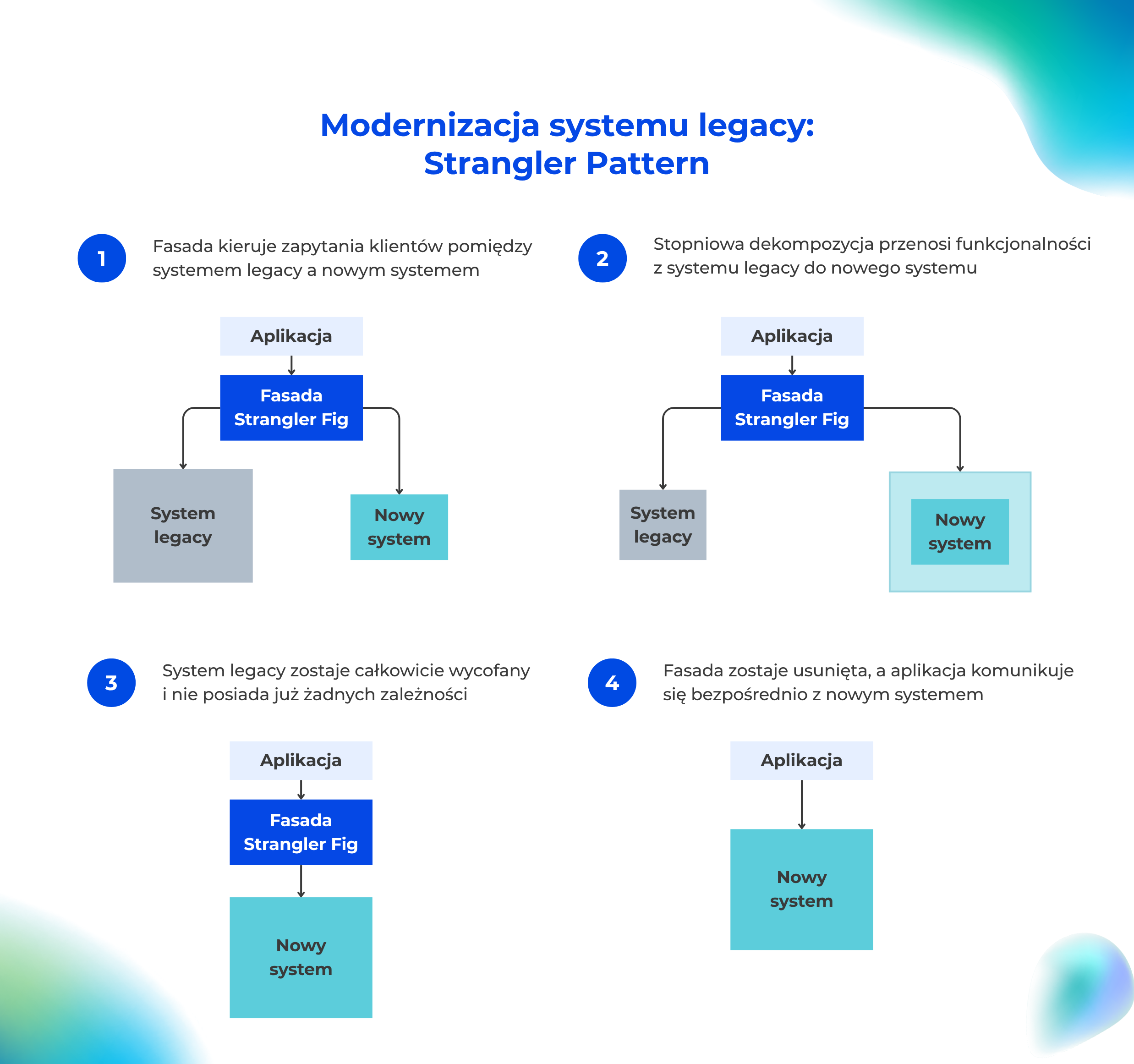
Strategy 3: Gradual Architecture Modernization – The Strangler Pattern
This is one of the safest modernization strategies for mission-critical environments. The strangler pattern works by: developing new functionality alongside the legacy system, gradually retiring old components, surrounding the legacy core with modern services.
A crucial element is automated testing before each iteration. This step is often overlooked. Comparative tests confirm that the new components behave exactly like the legacy ones they replace, ensuring that nothing is lost during the transition.
Benefits: minimized risk, continuous learning during the process, no single “critical cutover moment”.
Although it requires strong architectural discipline, this approach is highly effective when operational continuity is a priority.
Strategy 4: Functional Decomposition
Legacy systems often try to handle too many responsibilities at once. Decomposition focuses on: identifying independent functional areas, gradually extracting them into separate solutions, simplifying the system’s core.
As with the strangler pattern, each iteration should be supported by automated tests that confirm the correctness of the extracted components.
Result: reduced complexity, improved scalability of selected functions, easier development of new features.
Strategy 5: Process Modernization as a Starting Point
Sometimes the real problem is not the system itself, but the processes embedded within it. Before introducing technical changes, it is often worth: mapping the real business processes, identifying workarounds and manual steps, simplifying process logic.
Without this work, technical modernization often preserves existing chaos by transferring old problems into a new architecture.
Strategy 6: Full System Replacement
This is the most risky strategy, but sometimes unavoidable. It makes sense when: the system no longer supports critical business processes, maintenance costs are unacceptable, security risks are too high, the architecture prevents meaningful evolution.
The most common mistakes: attempting to replicate the old system 1:1, skipping the transition phase, underestimating data migration and process changes.
Replacing a system is a transformational project, not merely an IT task.
Which Strategy Should You Choose?
In practice, organizations often combine several of these approaches simultaneously. Different parts of a system may be modernized at different speeds, and strategies may evolve during the process. The key is to understand: the role of the system within the business, the acceptable level of risk, the clear objectives of modernization. Equally important is resisting the big-bang approach.
There is no single best strategy for legacy system modernization. However, there is a strategy that is right for a specific system, organization, and moment in time.
What’s next for your legacy system?
From assessment to implementation, we support organizations in modernizing legacy environments – helping evaluate risk, bring structure to IT landscapes, and implement changes step by step without disrupting business operations.
Process Inventory
Before you start modernizing – gain a clear understanding of your organization and its processes. Together, we identify bottlenecks and document key workflows.
IT Architecture Audit
We assess where improvements are needed in the performance and security of your systems – before they turn into real problems.
IT Consulting
We act as a technology partner at every stage of digital transformation, advising on the selection of the right technologies and solutions.
Custom Solutions
When off-the-shelf tools are not enough, we build software tailored to the current business needs of your organization.

