What are the risks of maintaining legacy systems?
Legacy systems rarely stop working overnight. In most cases, they continue to operate for years – until the cost of maintaining them begins to outweigh the value they deliver. Even more importantly, many risks build up gradually and remain invisible for a long time. That’s why below we outline the key risks organizations face on a daily basis.
1. Operational risk – “the system works… until it doesn’t”
The most dangerous legacy systems are those that are critical to operations, lack a real fallback plan, and are poorly documented.
What does this mean in practice?
- A failure in a single component can halt an entire process due to undocumented dependencies.
- Recovery time is difficult to predict, making business continuity planning challenging.
- Lack of regression testing increases the risk of uncontrolled errors – especially after changes.
- As a result, every production change becomes stressful and relies on improvisation.
2. Security and compliance risk
Older systems often fail to meet current security standards. They are rarely updated, rely on outdated authentication mechanisms, and offer limited audit capabilities.
The consequences are serious:
- Vulnerability to attacks increases with every month without updates.
- Meeting regulatory requirements becomes increasingly difficult.
- The organization is exposed to financial penalties and reputational damage.
- Control over data access becomes limited.
The longer a system remains legacy, the more expensive it becomes to “patch” security – making a proactive approach essential.

3. Knowledge (competency) risk
This is one of the most underestimated risks. Critical knowledge is often concentrated in the hands of a few individuals. At the same time, documentation is outdated or missing, making onboarding difficult. Moreover, the departure of even a single person can significantly disrupt system maintenance or development.
The result? The system becomes a black boxthat no one wants to touch.
4. Financial risk – hidden costs
Legacy systems rarely appear expensive at first glance. However, costs accumulate across multiple areas:
- Long lead times for changes slow down the entire business.
- Maintaining niche expertise generates ongoing costs.
- Teams spend more time fixing issues than developing new capabilities.
- Infrastructure costs continue to grow.
- As a result, new business initiatives are delayed or blocked entirely.
The most expensive part of legacy is not outages – it’s the lost opportunities.
5. Strategic risk
Legacy systems can limit the ability to introduce new products and make integration with business partners more difficult. They also hinder automation and scalability, forcing costly architectural compromises in new initiatives.
At some point, the organization starts adapting its strategy to the system – instead of adapting the system to the strategy. This reversal of priorities can significantly constrain growth.
6. Organizational and cultural risk
Legacy affects more than just IT – its impact is organization-wide. Over time, it leads to team frustration and a lack of ownership over solution quality. It also reinforces a culture of avoiding change because “it’s too risky.” As a result, innovation declines and employee initiative fades.
A system that was meant to support the business begins to limit accountability and creativity across the organization.
Why are legacy risks so hard to detect?
Primarily because they accumulate gradually and are distributed across multiple teams. They often have no single owner, which means no one feels responsible for monitoring them. Moreover, they tend to surface only in crisis situations – when responding is the most difficult.
And by then, it is usually already: more expensive, more complex, and far riskier.
Legacy Documentation Automation
Knowledge about your
system architecture can update itself
Wiedza o architekturze systemu może aktualizować się sama
Instead of manually rewriting code structures and wasting time in Confluence, implement S*.doc.
Our AI agents automatically map your application architecture, while your team gets a RAG bot integrated with Microsoft Teams that can answer any question about the system directly from the source code.
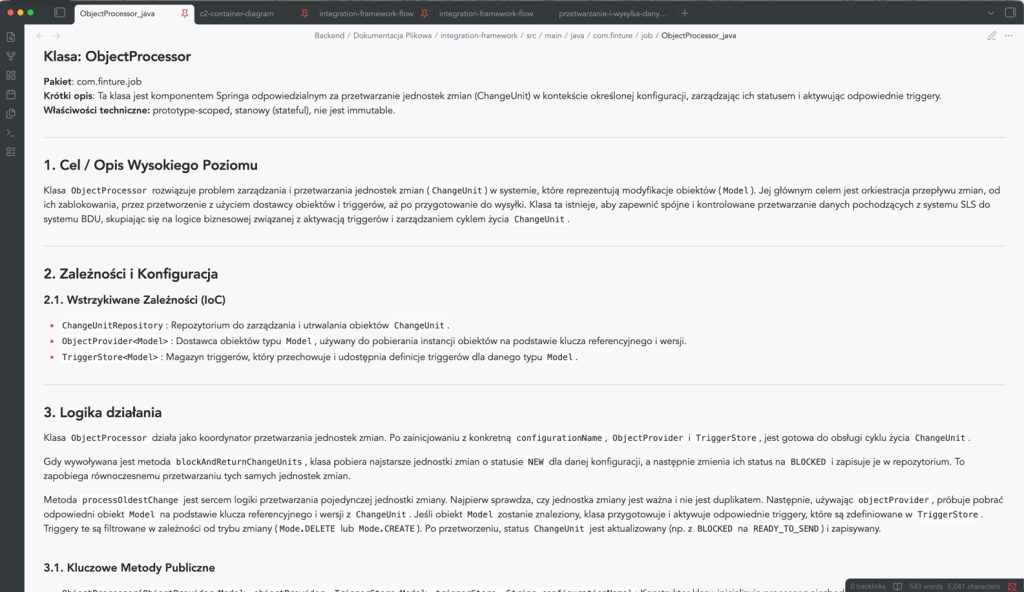
Automatic generation of Java/C# documentation
Code documentation
Generated automatically, taking into account the specific features of the programming language – Java, C#, TypeScript, C++. It divides the content into logical sections, omits irrelevant elements and allows you to tailor the type of documentation to the audience: technical for developers or simplified for end users.
- A clear, structured description of each module
- Automatic skipping of boilerplate and generated code
- The ability to generate a report on compliance with safety guidelines or a report on technological optimisation
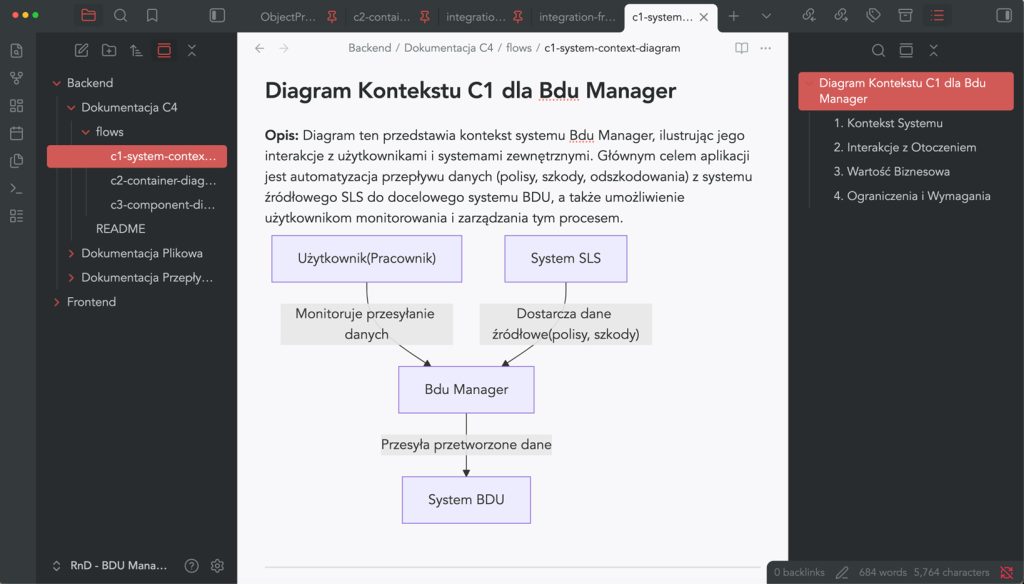
Architectural visualisation of C4 & Mermaid
Architectural documentation in accordance with the C4 model
S*.doc automatically generates Mermaid diagrams for the context, container and component views – in accordance with the widely recognised C4 model.
So, no more manually drawing diagrams that become outdated after the first sprint.
- Consistent visual representation of the architecture at various levels of detail
- A clear presentation for the board, auditors and new team members
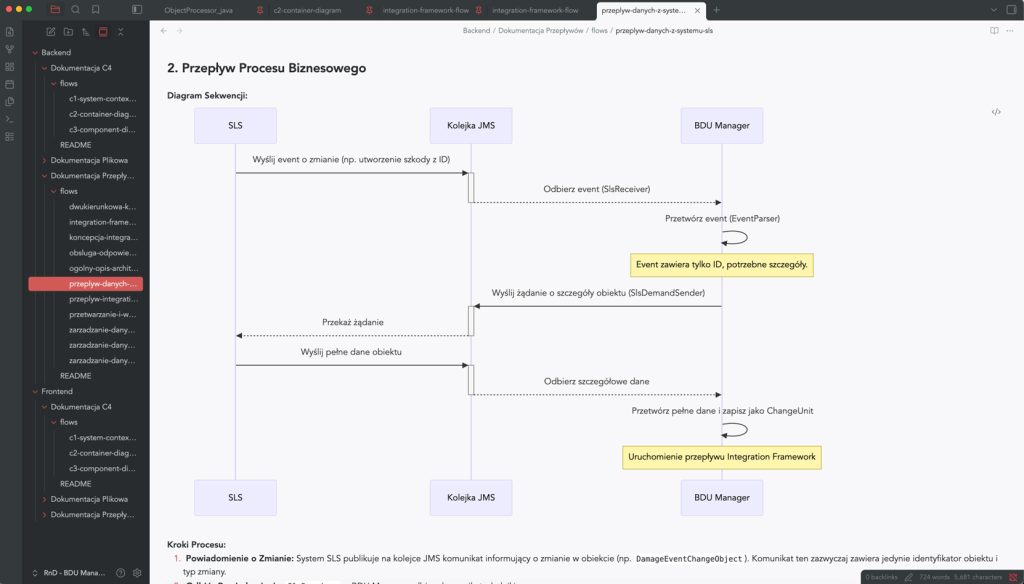
Business Process Mapping (BPM)
Business process documentation
S*.doc models the flows within the system and how its components interact – process steps, interdependencies between components, and data exchange points.
Instead of asking, “How does it work with other things?” – you can check it out in 30 seconds.
- Visualisation of user journeys and communication between services
- A description of the internal logic in language that is understandable to both business and technical staff
- Support for retrospective code reviews and dependency analysis